Diane’s farewell message
After 52 years at WAMU, Diane Rehm says goodbye.
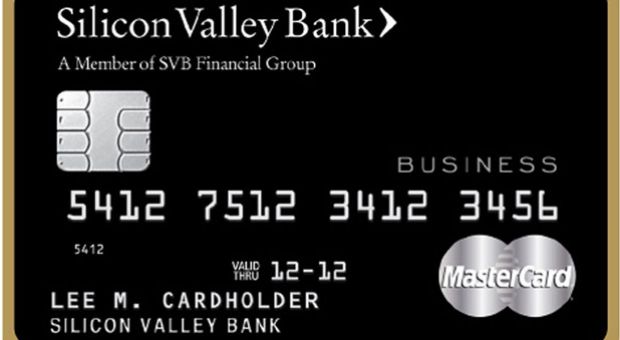
Silicon Valley Bank is the first to deliver chip-enabled credit cards, with EMV chip technology, to businesses in the U.S.
Target and Neiman Marcus are the latest retailers to reveal security breaches that put customers’ credit and debit card data at risk. But experts say it’s far more common than we’d like to think. Hundreds of data breaches were publicly disclosed last year alone. Yet the U.S. is far behind European and other nations that use more sophisticated chip-and-pin technology to thwart hackers. This week, U.S. lawmakers called for a congressional inquiry into credit card data theft. And major American retailers and card issuers have plans to adopt more secure technology. But many warn more needs to be done. Diane and a panel of experts talk about how to make credit and debit cards safer.
MR. DIANE REHMThanks for joining us. I'm Diane Rehm. Credit card experts say small-scale data security breaches are common. The one experienced by Target last month was notable mostly for the size of the theft. About 40 million credit and debit card records were stolen from that retailer. Neiman Marcus also revealed a significant breach.
MS. DIANE REHMHere in the studio to talk about safeguarding Americans' credit and debit card data: Doug Johnson of the American Bankers Association, and Shane Sims of PricewaterhouseCoopers, from an NPR studio in New York, Robin Sidel of the Wall Street Journal, and, by phone from Bella Vista, Ark., Mark Horwedel of the Merchant Advisory Group. I'm sure many of you have your own questions. Give us a call, 800-433-8850. Send us your email to drshow@wamu.org. Follow us on Facebook or send us a tweet. Welcome to all of you.
MR. DOUG JOHNSONThank you.
MR. SHANE SIMSThank you, Diane.
MR. MARK HORWEDELThanks for having us on today. Appreciate it.
MS. ROBIN SIDELHello.
REHMAnd, Robin, if I could start with you, tell us what we know so far about these data breaches that occurred at Target and Neiman Marcus.
SIDELWell, we don't know that much about what happened at Neiman Marcus. They haven't really released a lot of information. We know a lot more about Target. And there was malicious software known as malware that got into their system. And that's where the bad guys got in and pulled out the data from credit card and debit card customers. And then the company also revealed that there was a breach of other data as well, email addresses, regular addresses and names that was separate from, actually, the credit card incursion.
REHMAs I understand it, the Neiman Marcus breach occurred more than a month ago. How come we're just learning about it?
SIDELWell, I think that retailers often don't know exactly how to handle this. I mean, first of all, it takes a while for them to figure out what has gone on. And then they don't really know the extent of it. So there's always this internal battle at a company about when you publicly disclose something and even if you need to publicly disclose something because there are a lot of these breaches that happen that you and I never know about.
REHMRobin Sidel of the Wall Street Journal. Turning to you, Shane Sims, how does this happen? At what point? Explain to us what it is that occurs to create the theft.
SIMSSo what happens is these criminals from all over the world will target an organization. And they'll go through a multi-step process to accomplish their objectives, which in this case is the theft of payment card information.
REHMWhat do you mean a multi-step process?
SIMSSo step one for them will be to do some reconnaissance of systems that are used on the Internet by the Target organization. So whoever they are targeting to steal the information from, they're going to understand that their attack service looks like.
REHMHow long does that normally take?
SIMSI would say that takes days to weeks.
REHMOK.
SIMSTo really establish what the attack service looks like. And then once they find a vulnerability with those systems, they will exploit that vulnerability and then have access to the target network.
REHMSo explain exactly where the theft occurs and how.
SIMSYeah. So once they achieve access to the network, they begin to explore the inside of the infrastructure of the organization they've targeted. And they will look for systems that have the information they want. And a lot of times -- and in the case that we're dealing with here -- the point-of-sale systems contain the information that the attackers are after. So they will actually navigate to those systems and install malwares Robin mentioned on those systems to get the information.
REHMNow, I gather there's no way for a company to know that somebody has even targeted it before the thefts begin.
SIMSWhat we typically see is the criminals get into the environment, and they're inside the network for days to weeks trying to understand where the data is and establishing their foothold. And the organizations do not know this activity is going on.
REHMI gather that you were a special agent for the FBI for 10 years, focusing on cybercrime, so you've seen this happen many times.
SIMSI have. I've been involved in cybercrime since it began in the '90s. And I've had an interesting seat to witness how criminals have evolved over time. And I think what we're seeing here are very organized groups. They're very sophisticated. They understand how companies secure their information. And they work very hard to plan and develop ways to circumvent that security.
REHMNow, what happens once they glean this information? How do they then use it?
SIMSWell, they use it in a variety of ways. So we often see that the theft of credit card information or payment card information in general is then sold on the black market and on the Internet. And there's value to each unique account number in all the data that would be contained on the mag stripe, the magnetic strip on the back of the credit card or debit card. So these criminals can actually profit from selling the data that they've stolen. Or they can use it themselves to then commit various frauds, like credit card fraud.
REHMShane Sims of PricewaterhouseCoopers. And now to you, Doug Johnson of the American Bankers Association. If your credit or debit number is stolen without your knowledge and somebody makes a purchase, what's the liability to the consumer and to the bank?
JOHNSONWell, the liability to the consumer is really zero in most cases because the bank will reimburse.
REHMIf it's a credit card purchase.
JOHNSONOr if it's a debit card purchase. I think the difference is, is that, to the extent that it's a debit card purchase, the transaction may actually end up on the account and the customer may not be aware of it. And so they may end up having some other transactions and may overdraft their account based upon the fact that they were not aware those transactions occurred. That's the difference. If there's fraud on the account, regardless whether or not it's debit or credit, essentially the customer will be made whole and reimbursed by the financial institution.
REHMBut I gather you've got to be responsible for notifying the bank pretty quickly.
JOHNSONAbsolutely. You should always be evaluating your account, not just your account statement but also your online account because that's where you're going to see the unauthorized transaction most quickly. Don't wait for your monthly statement. But if you do wait for your monthly statement, you still do have 30 days to make that -- to the extent that it's a transaction that wasn't caused by the fact that you lost a card. If you've lost your card, immediately contact your financial institution because you only have several days to be able to do that, to the extent that you know the card was lost.
REHMIs it better to use a credit card or a debit card?
JOHNSONWell, every customer is going to have their own preference. But I think that clearly, as I just described, there is some additional potential consumer pain when you're talking about a debit card because there may be that unauthorized transaction on the account, you may not be aware of it, and because of that, you may end up overdrafting your account.
JOHNSONBut to the extent that you're someone that evaluates your account on a continual basis -- and that's what we really recommend -- and you see that transaction immediately, you can refute that transaction, and then it won't cause you any particular harm on the debit side.
REHMShane Sims, Forbes posted an article on its website yesterday titled, "Why Even North Korea Outpaces the U.S. in Credit Card Security." Talk about the so-called EMV cards that are available in Europe and even in North Korea and why we don't have those here.
SIMSI wish I had an answer to that question. And Doug may have one for us, but, yeah, the Chip and PIN, as it's referred to on these cards that are being used in Europe, just gives the consumer an extra layer of protection. I think you can call it multi-factor authentication as a way to describe it. So when you execute the transaction, you have to have the chip that's on the card present for the transaction.
SIMSAnd the consumer has to enter a PIN. So there's two factors there, and it makes it more difficult if the criminals were to actually steal the credit card information to then actually commit the credit card fraud.
REHMSo from your view, Doug, at the American Bankers Association, why is it that we don't all have those EMV cards, providing at least one more layer of security?
JOHNSONWell, first of all, Diane, in our country, we didn't legislate it. And I think that's the first piece. Secondly, we have a large economy. We've got thousands of financial institutions. I think, going forward, we both, as bankers and as retailers, have an obligation to move as swiftly as we can toward EMV, to put that other layer of security in there. And I think that, yeah, there's expenditures that are going to have to be made on both sides. And I think that's what we need to do.
REHMMark Horwedel of the Merchant Advisory Group, would you like to see that EMV technology in place as soon as possible?
HORWEDELYes. I think that I would add that the current plans to move to EMV in the U.S. need to be supplemented some additional steps that so far are not a part of the EMV road maps that major card networks have focused on. So we want to see a holistic approach that includes a number of other steps as well.
HORWEDELAnd I think, as Mr. Sims pointed out, one of the foremost steps is that U.S. consumers should be equipped with a PIN, whether we're talking about a debit card or a credit card, so that, again, I think, as he said, it's not just about having something that you're carrying with you, a card or some other device, but you also have something that you have to know a PIN.
REHMAll right. Mark Horwedel of the Merchant Advisory Group. Short break. More on that when we come back.
REHMAnd welcome back. We're talking about credit card theft, the big data theft that occurred at Target during the Christmas holidays. And now we have learned that Neiman Marcus had a breach of security as well. Doug Johnson is here in the studio. He's with the American Bankers Association. Shane Sims is a partner at PricewaterhouseCoopers.
REHMRobin Sidel is on the line with us. She's with The Wall Street Journal covering the credit card industry. And by phone from Bella Vista, Ark., Mark Horwedel of the Merchant Advisory Group. Mark, I want to come back to you. You were telling us that you feel that there have to be some additional steps taken in addition to that chip, such as...
HORWEDELRequiring a personal identification number or PIN on every transaction, that's been the rule throughout most of the rest of the world most recently. In Canada, when they converted to EMV, while they had PINs on all their debit cards prior to the conversion, they added PINs to all their credit cards as well. And the merchants feel very strongly that that step needs to be taken in addition to those that have been outlined by the card brands so far in order to more thoroughly protect the U.S. consumers.
REHMRobin, I wonder if you would talk about the timeline for widespread adoption of this EMV technology here in the U.S.
SIDELWell, as of -- some rules came out from Visa and MasterCard a couple of years ago. And as of 2015, the liability will shift to merchants. Right now, if there's fraud, the banks pick up the tab. And by 2015, that liability will shift to merchants. But this is a battle that has been going on for years. And it bubbles up and then calms down. And obviously it's situations like this where there's a very public breach that it really bubbles up and people start talking about it again. But the credit card industry and the merchants have been fighting over this issue for years.
REHMSo, Mark, in your view, is that 2015 deadline on the shift of responsibility from the banks to the merchants going to speed up the process?
HORWEDELIt'll speed up the process. It's an impossible date to make. Many merchants simply cannot make that date. There aren't even enough resources, frankly, at...
REHMWhat resources are necessary? Explain.
HORWEDELWell, the resources -- I was about to refer to the resources even at Visa and MasterCard and the processing -- third-party processors that do business with the merchants in the U.S. to thoroughly test and certify the entire merchant community in the U.S. before that date.
REHMI don't understand. I wonder, Shane, if you would explain.
SIMSI'm not sure actually. What we're dealing with here is a crime wave that has evolved over the last decade. And it's going to get worse over the next 10 years. It's not going to slow down. We have to do something. We need to step up the protection of the consumer. And we need to help organizations in the private sector help protect their networks and where the information exists because this crime wave is really going to get worse.
REHMDoug Johnson, what is the hardware and the software that need to go into place to create a safer use of the credit card?
JOHNSONWell, first of all, on the card itself that the banks issue, there will be a chip on that card. And...
REHMNot until 2015?
JOHNSONWell, some institutions -- an increasing number of institutions, they're already deploying the chip on the card.
REHMWho?
JOHNSONWell, Bank of America, for one, has the card. There's a number of other institutions and some credit unions that have the card deployed as well. And you'll see an increasing number of those institutions over time doing that. And institutions also have the responsibility by fall of 2015 to put EMV on their ATMs. And so that will actually protect the ATM because that's where there's a great vulnerability to bank customers because you can do a direct cash out as opposed to having to buy merchandise. And so that's another piece of protection that I think is very important.
REHMWhen you say a direct cash out, explain that.
JOHNSONSo in -- let's use the Target breach as an example. If, in fact, the PIN was compromised and not encrypted or decrypted so the criminal has essentially the account number and the PIN, well, then essentially that criminal can go to an ATM -- any ATM and essentially have access to that individual's account. And so they don't have to go through that process of having to buy merchandise and fence merchandise or do things of that nature, which sometimes happens on the criminal side.
JOHNSONSo that's why as part of this movement toward EMV, it's important to also protect the ATM environment because a breach at a retailer can also make the customer vulnerable at that ATM.
REHMRobin, talk about the politics behind all this. What is the delay?
SIDELWell, it's a real chicken-and-egg scenario. And the banks and the merchants need each other, but they also fight over a lot of things in this industry. And it's just been going on for years. The banks -- it's expensive to issue these cards for the banks, and so they don't want to issue the cards until the merchants have the hardware and software in place. And the merchants say they don't want to turn the switch and get this stuff in place because nobody has the cards. So it's a classic chicken-and-egg situation. And they've been fighting over it, as I said, for a very long time.
REHMIs there any estimate on how much the adoption of the EMV card could reduce the risk of fraud?
SIDELI think the view in the industry is that it would be significant. I was speaking with a senior executive in the credit card industry yesterday. And the problem is, as he said, everybody knows that the U.S. is more vulnerable than other parts of the world, so the fraudsters are coming to the U.S. And so if you make it an even playing field, that's going to be less likely to happen. The U.S. won't be the only target. And, look, nobody knows if the chip and PIN is going to be the salvation that people think it is. I mean, the bad guys are pretty smart, and they keep coming up with new ways to infiltrate the system.
REHMSo right now, the question is, who's going to bear the cost of changing the system, Robin?
SIDELThey both will. They both have to. I mean, you know, the banks have started issuing some of these chip and PIN cards but a very, very small amount. And they're actually only really issuing them to people who travel frequently abroad. So if you have a travel credit card or one that's an airline credit card perhaps, that signals you travel a lot. And so they're issuing them to those people -- it's a small group -- to make their life easier when they go abroad. But it's millions and millions of dollars for both the banking industry and the merchant industry.
REHMDoug Johnson, you already have a credit card with that chip installed. Had you used that card at Target, would you have been protected?
JOHNSONWell, we don't know at this particular juncture because there's some question as to whether or not the PIN information, when it was compromised, was encrypted which would make it very difficult for someone to decrypt or whether or not it was plain text, which would allow someone to have that PIN information and then be able to essentially, you know, use that information. I think that what EMV does is it makes a random number associated with the transaction.
JOHNSONAnd so if, for instance, Target had their point-of-sale device where you swipe -- EMV enabled and you swipe it, that transaction has a unique number associated with it. And that card has a unique number associated with it for that transaction, so you can't use -- you can't duplicate that because the chip is what's making that random number essentially. So there is an extra level of protection, Diane, that would've existed to the extent that EMV was in place both at the point of sale as well as on the card.
JOHNSONNow, if the card was enabled and the point-of-sale device wasn't, well, then you don't have full protection. And that's why when we fully implement this on a voluntary basis toward the end of next year, if the retailer does not put the point-of-sale device in place as EMV enabled, they have the liability.
REHMI see. Mark, you might just talk about how retailers who are -- who had their security breached, such as Target and Neiman Marcus, how does this affect them?
HORWEDELIt creates a lot of problems. It's probably more reputational damage than anything else because consuming public is concerned about the security surrounding the use of their cards. And so it's -- you know, it's a very costly event for merchants. I would suggest much more costly than from anybody else's perspective associated with payments.
REHMHere's an email from Russ in Punta Gorda, Fla. "Please ask why the people that have credit cards and debit cards in the U.S. should not be given the chip cards. Everyone in Europe has. Last year, I was in a restaurant in France where the card reader would not take my swipeable card, so I had to pay cash and go to the place down the street where my magnetic strip could be read to replenish my cash." So, Robin, how long have these EMV cards been available in Europe and elsewhere?
SIDELFor a long time, for years, and just increasingly. It's usually kind of a staggered process where they adopt them country by country. And Canada has adopted it in the past couple of years as well. And that's -- the person who wrote in, I mean, that is an issue, and that is why, I guess, his credit card company -- maybe they didn't travel often enough to kind of be in that group that gets one of these cards from his U.S. credit card company.
REHMDo you want to comment, Shane?
SIMSYeah, I totally can sympathize with the person that posted that question. It's happened to me, too, traveling overseas. And it's very frustrating for consumers. And it's very concerning for consumers when these merchants have these breaches, even though, as we've learned here today from Robin and Doug and Mark, that there's really no impact -- no financial impact to the consumer. That doesn't change the fear factor. And it's really, really important that we begin to do something, whether it's the chip and PIN and/or improve security on the backend of these merchant environments.
REHMWell, indeed, as Doug has pointed out, these folks who've had their security compromised could, in fact, have their ATMs compromised as well. So whether in fact they're really hurt remains to be seen. And you're listening to "The Diane Rehm Show." I'm going to open the phones, 800-433-8850. First we'll go to, let's see, David in Lebanon, Ohio. You're on the air.
DAVIDThank you, Diane. Great show today so far.
REHMThank you.
DAVIDI'm not terribly objective because I work for an insurance company that insures credit unions against losses due to credit and debit card, just like we're talking about right here. And I know we've weighed in quite a bit on how this has impacted the consumer and the merchant to a degree. But what nobody really talks about -- and it always irks me -- is that the credit card brands themselves, Visa and MasterCard, have almost no downside on this, almost no responsibility when it comes -- monetarily when it comes to these losses.
DAVIDAnd that's always irked me that they just keep pushing to make it easier and easier for consumers to use their cards to the detriment of the merchants and the financial institution.
REHMThat's interesting. How do you respond, Doug Johnson?
JOHNSONWell, the networks themselves are responsible for putting together the operating rules associated with the use of the cards. And so I agree that the liability isn't there. I think their responsibility is to really ensure that there's a proper level of information security requirements for merchants and for banks. And that's what's called the payment card industry data security standard. But I think that, you know, from the network's perspective, that's really their job is to try to build a consistent set of security requirements for the network and to ensure that the network works seamlessly.
REHMMark, do you want to comment?
HORWEDELI think that they do suffer damage from the standpoint of the impact on their brands and, you know, the views of consumers about using their cards. I would say, however, that when these breaches occur, merchants pay a tremendous amount of money to the brands by way of PCI fines. And so, you know, indirectly they profit from this.
REHMAll right. Thanks for that. And let's go to Grants Pass, Ore. Marcus, you're on the air.
MARCUSYes. Hi, Diane.
REHMHi.
MARCUSJust wanted to say how much we love your show. I listen to it every day on the way to work.
REHMThank you.
MARCUSIn fact, I'm on the way to work right now to the hospital.
REHMGood.
MARCUSAnd, you know, as a frequent traveler to Europe -- we have a home in Switzerland. My dad immigrated here to the United States many years ago. And we still have family. We go there quite often, at least once a year, sometimes twice a year. And, you know, it gets really, really frustrating now when you have to go to the grocery store, and you can't buy things in the grocery store because your card doesn't get read anymore.
MARCUSAnd the United States has made it very, very difficult for American citizens to get bank accounts in Europe. And so now you have to take cash. And, you know, traveler's checks are Stone Age, so...
REHMAll right. So what you want to know is how you can get a credit card that would work there, right?
MARCUSExactly, and, you know, why we can't get them. I know since I've been on hold waiting a little while, you know, you've discussed that, but it's just another...
REHMOK. All right. Let's see what the response is, Doug Johnson.
JOHNSONWell, I think that the European traveler was the first one to get the cards among United States citizens. And I agree with their frustration. I think that clearly we have an imperative to try to employ additional cards as fast as we possibly can. That's...
REHMSo can one simply apply for a card to...
JOHNSONIn many financial institutions. You can at your financial institution, yes.
REHMAll right. We're going to take a short break here. When we come back we'll hear more, take your calls. Stay with us.
REHMAnd we're back discussing the thefts that have occurred through use of credit cards, debit cards. Here's an email from Pete, this one for you, Shane Sims. "How do the merchants detect a theft event?"
SIMSThere's many ways they could detect it. So if you go back to my discussion earlier about there's these different steps or different phases to a cyberattack, the first step is reconnaissance. So, you know, the criminals are looking for systems and looking for security holds on systems. That's a detection point. Once the criminals get access by exploiting one of these security holds, they install malware or this malicious software on the systems.
SIMSThat's a detection point. When they actually collect the payment card information and transfer it out of the environment to a system on the Internet that the criminals control, that's a detection point.
REHMBut somebody's got to be watching at all those points.
SIMSIt's very difficult. And the moral of the story is, most of the time detection comes by way of a third party. So either...
REHMWhat does that mean?
SIMSEither law enforcement notifies the merchant or the banks are triangulating all this credit card fraud back to a common point of purchase. And then they notify the merchant.
REHMSo it's after the fact.
SIMSAfter the fact.
REHMAlmost everything is after the fact, Doug.
JOHNSONI think it is true that financial institutions spend a lot of time talking amongst themselves to find that common point of compromise. We see authorized transactions that are reported to us by our customers. Those transactions obviously wouldn't have been at the store that was compromised. And so it's trying to find exactly what that common point of failure is. And so I think that's right that we end up, in a lot of cases, informing the retailer that we found that.
REHMAll right. And here's another from Michael in San Antonio. "Please discuss the likelihood that these breaches are inside jobs conducted or facilitated by the retailer's employees. And why don't banks and retailers do more to protect consumer information?" What about the possibility of an inside job, Shane?
SIMSThat's a very interesting question. And PricewaterhouseCoopers does a global information security study every year. And over the last three or four years we've seen this insider threat concept rise up in the study as a concern. And when we're doing our investigations of these breaches, we consider that as an element of the crime.
SIMSYou know, did an insider who had knowledge of how that network operates, were they colluding with the outside criminal organization? We have had some situations where insiders were at risk of colluding. Most of the time, from our perspective, though, all of these jobs are committed by an external threat actor.
REHMAnd in the case of Target, is your assumption or is the evidence thus far leading to someone outside the United States?
SIMSMy knowledge of that incident is strictly through the news media. And from what I've read and what I've seen it would indicate that it's an outside job.
REHMRobin, what do you know?
SIDELWell, I think one of the other potential risks in these kinds of situations are outside vendors. And companies like Target use a lot of outside vendors for all different things with their systems. And...
REHMGive me an example. Give me an example.
SIDELWell, a vendor who will help safeguard or monitor or update their point-of-sale device. They use outside companies for a lot of these different things, so that kind of broadens the potential places where this incursion could've occurred. And so that's one thing I think people in the industry are very concerned about, not only it being somebody from the inside who had that access, but there are a lot of people from the outside who also can have that access and, you know, act in cahoots with an organized group.
REHMMark Horwedel, Congress has called for an inquiry into the Target data breach. Do you expect any widespread changes to be made?
HORWEDELYou know, it's hard to know until, you know, we actually get into the middle of if there is in fact a committee hearing on the subject. I suspect that, you know, something like that might well lead to the discovery that there are other places where we can go to make the payment environment safer, many of which frankly we've advocated as a part of the conversion to EMV.
REHMAnd, Doug Johnson, what could lawmakers do to make this process more safe?
JOHNSONWell, I think that a lot of the discussion is around trying to build a national data breach reporting standard because one of the things which is currently true in our environment is there's a variety of state laws that companies have to abide by and financial institutions have to abide by in terms of breach notification.
JOHNSONAnd I think there needs to be some clarity there so we have swifter notification of those breaches. Clearly I think that there's a necessity also to ensure that all the partners within the payment system have a comparable level of security. That's what the payment card industry data security standard is supposed to accomplish.
JOHNSONBut I think that one of the things that we see within the financial services environment right now is that there's a lot of attention being paid to those third parties that we've been discussing here on this call. And I think that there could be some value in having retailers have that same level of attention to their partners that are part of the payment process.
REHMSo what if Congress passed a law saying that every credit card issued should have this EMV chip in it and ordered that by say the end of 2015, every retailer had to have that mechanism in place to read that card here in the U.S.? What might congress be able to do there?
JOHNSONWell, if Congress was to put that in place, it would be actually frankly very similar to what the networks are trying to do on a voluntary basis through their guidelines. Institutions and retailers are not going to be specifically required to have EMV in place by the fall of 2015. But if they don't they have to incur additional liabilities associated with those transactions. Right now...
REHMBut of course they'll be insured, so they'll put it off onto the insurance companies.
JOHNSONAnd the insurance companies will make some determination as to whether or not there was any negligence associated with that particular breach. So you get into that process as well.
REHMAll right. Let's take a call in Richardson, Texas. Hi Seena, you're on the air.
SEENAHi, Diane. Thank you for taking my call.
REHMSure.
SEENAI actually have a second question that's come up while listening to your show. The reason I called was in regards to the financial benefit. Obviously this type of crime is done due to somebody trying to make money. And my question is, how much money is made by reissuing the credit cards and all of the hassle that everybody has to go through to correct the situation?
REHMI'm not sure I understand the question.
SEENAWell, when this happens and -- like, I myself am in a situation that I can't use my card for much of anything at this point. I have to wait for...
REHMWhy?
SEENAI have to wait for a new card to be issued to me.
REHMUsually they issue cards within 24 hours.
SEENAWell, mine's taken over a week, and I know a lot of people, it's taken over a week at this point because there's so many that have to be reissued. What is the financial benefit -- who makes the money by having to reissue these cards?
REHMDoug Johnson.
JOHNSONWell, banks certainly don't make money by reissuing cards. There's essentially a substantial cost associated with the reissuing of those cards. It could be as much as $10 a card when you put in all the various costs associated with that. So I would certainly not call it a money-making operation. It's actually something that's very costly to financial institutions.
REHMRobin, from your point of view, what can consumers do to protect themselves against fraud?
SIDELWell, I think we've discussed that a bit. And, you know, obviously you really need to pay attention to your statements, to your online account, looking at your transactions. And while debit cards are also zero liability, if someone takes that money out, as we discussed before, that money can be gone and it could take a lot longer time to replace it. So a credit card, if you didn't make that purchase, you don't have to pay. But a debit card, that money's already gone.
REHMOK. What about all the online apps and shopping, Shane Sims?
SIMSYes. You know, as businesses continue to grow and expand and try to leverage the Internet to the best of their ability, it extends their attack surface. So the attack surface gets bigger. And as mobile apps go out...
REHMYou mean, if you have an app on your cell phone.
SIMSExactly. So that's just another point where criminals are looking to exploit so they can get access to the consumer's information.
REHMBut it's interesting because those apps can offer real economic savings to a consumer. So that's why they're so popular.
SIMSNo doubt. I mean, I'm a fan myself as a consumer. And I think the moral of the story here for businesses and merchants is that security has to be baked into the business strategy. So as you expand your business and think about your business in a creative way, security has to be a part of that discussion.
REHMWell, I'm not sure where you're leaving me. If someone shops at a particular grocery store, for example, Safeway here in the Washington area, Safeway has an app that offers greater savings to individuals. Are you saying that it's Safeway's obligation to put in more security with that app than normally they'd have just at the point of purchase?
SIMSYes. Securing the information that you're collecting from a consumer is an obligation of the merchant. So -- and I think this goes back to a point that came up earlier that we might've lost here a little bit, is that we've talked about payment card information being stolen. But a lot of consumers are very, very concerned and worried that if criminals have access to these merchant networks, that their personal identities may be at risk, too. And I think in the example that you just mentioned, that's a very, very true risk that consumers have.
REHMAnd of course Edward Snowden has shown all of us that nothing is safe. Would you agree?
SIMSNo doubt. He -- that situation has brought the insider threat angle, you know, back into the forefront of senior executives.
REHMDoug Johnson.
JOHNSONI just think it prudent for individuals to just use every tool they have available to protect themselves.
REHMAre you saying, don't use apps?
JOHNSONNo. I'm saying, look very carefully at your transaction activity.
REHMBut that's after the fact.
JOHNSONAnd it is after the fact, but it shouldn't stop you from making the transactions, because by and large 99 percent of those transactions are -- and more than that are going to be perfectly fine. That's why you monitor accounts on an ongoing basis. There's risk everywhere in the world. This is a very real risk. It's a risk that's going to continue to increase.
REHMDoug Johnson of the American Bankers Association, and you're listening to "The Diane Rehm Show." Let's go to Jordan in Charlotte, N.C. You're on the air.
JORDANHey, thanks, Diane.
REHMSure.
JORDANI appreciate you talking about this. There's one thing I haven't heard the whole time since the Target breaches, who the culprit is. And with, you know, the focus on technology being the first defendant against our, you know, financial safety, who did this and how much money did they make off of it? And isn't there a vested interest in us finding out, you know, exactly who this culprit was?
REHMSure. Shane, how far along are we in that knowledge?
SIMSYeah, that process takes a very long time for law enforcement to understand, you know, the actual people, the human beings that executed this attack. It could take months to years. And one of the advantages of cyber crime itself is that you can be anywhere on Earth. You know, you could operate from a country that makes it very difficult for U.S. law enforcement and U.S. agencies to cooperate with those countries and bring people to justice. So it's a very, very difficult challenge, but I know that the law enforcement agencies here in this country are working very hard to make that happen.
REHMRobin, do we have any idea how much money is involved?
SIDELWe don't at this point. There's a lot of rumors and speculations that these -- some cards have already gone onto the black market. Obviously it's the black market. It's very hard to track, but there's certainly the sense that this is real. JPMorgan Chase was very concerned about the prospect of fraud.
SIDELAnd so they reissued 2 million debit cards, which is very unusual for a bank to do, because they usually don't like to reissue cards until there's real evidence of fraud. And sometimes they would rather take the risk of fraud than to pay for reissuing cards. But it was enough of a concern that a big bank like Chase reissued 2 million cards. And that's really saying a lot.
REHMDoug.
JOHNSONYes, it is saying a lot. I think that institutions don't want to inconvenience their customers to the extent that they feel they can monitor those accounts and look for unusual activity. And so in this case, obviously because of the very breadth of the breach, different institutions took a very aggressive approach, or the approach that made the most sense for them. But when you have on the order of 10 percent of your client base essentially impacted by this, that's pretty serious business.
REHMAnd, Mark, what about the retailers involved? How much do you figure they will lose in dollars, or is it simply reputation?
HORWEDELNo. It's -- there are severe fines and penalties that are leveled on the retailers that are involved in this that this happens to. And the reputational problems go on top of that.
REHMAll right. So last words, look at your statements every single month very carefully. Use your credit cards thoughtfully. But there's no way you're going to know at point-of-sale whether your information is being compromised. Is that a fair statement?
SIMSThat's a very correct statement, Diane.
REHMAll right. Shane Sims of PricewaterhouseCoopers, Doug Johnson of the American Bankers Association, Robin Sidel of the Wall Street Journal and Mark Horwedel of the Merchant Advisory Group, thank you all so much. And thanks for listening, all. I'm Diane Rehm.
After 52 years at WAMU, Diane Rehm says goodbye.
Diane takes the mic one last time at WAMU. She talks to Susan Page of USA Today about Trump’s first hundred days – and what they say about the next hundred.
Maryland Congressman Jamie Raskin was first elected to the House in 2016, just as Donald Trump ascended to the presidency for the first time. Since then, few Democrats have worked as…
Can the courts act as a check on the Trump administration’s power? CNN chief Supreme Court analyst Joan Biskupic on how the clash over deportations is testing the judiciary.