Diane’s farewell message
After 52 years at WAMU, Diane Rehm says goodbye.
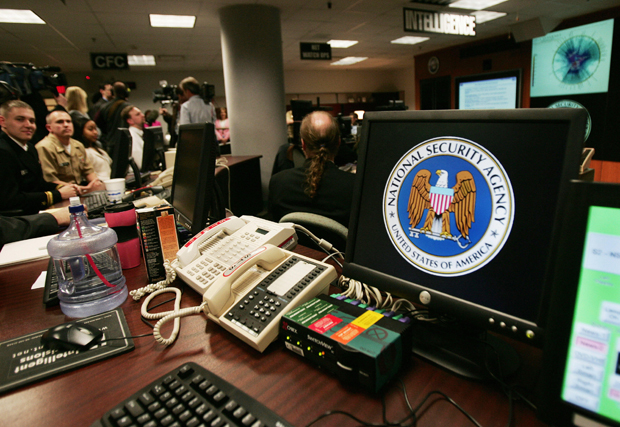
This file photo shows a computer workstation bearing the National Security Agency (NSA) logo inside the Threat Operations Center in Fort Meade, Maryland.
Most Americans had no idea the U.S. government was conducting a daily dragnet of their phone records until two years ago. That’s when Edward Snowden made this and several other NSA operations public, sparking a firestorm. Last week, a federal appeals court ruled that the Patriot Act, as written, doesn’t allow this practice. Now it’s up to Congress to make a decision. Senate Majority Leader Mitch McConnell (R-Ky.) supports re-authorizing bulk surveillance for five years, but a bipartisan group in the House is pushing for changes. If Congress doesn’t act, the program expires on June 1. We look at the future of the Patriot Act and what it means for your privacy and security.
MS. SUSAN PAGEThanks for joining us. I'm Susan Page of USA Today sitting in for Diane Rehm. Diane is recovering from a voice treatment. The mass collection of Americans' phone records revealed by Edward Snowden in 2013 could be coming to an end. Last week, a federal appeals court ruled it was illegal and Congress is struggling to reach an agreement on revising and renewing the program before it expires at the end of this month.
MS. SUSAN PAGEJoining me to talk about changing notions of privacy, security and the future of the Patriot Act, Benjamin Wittes of The Brookings Institution, Laura Donahue of Georgetown University Law School and Devlin Barrett of The Wall Street Journal. Welcome to "The Diane Rehm Show."
MR. DEVLIN BARRETTHi.
MS. LAURA DONOHUEThank you.
MR. BENJAMIN WITTESThanks for having us.
PAGEWe invite our listeners to join our conversation later in this hour. You can call our toll-free number, 1-800-433-8850. You can always send us an email at drshow@wamu.org or find us on Facebook or Twitter and leave a comment. Well, Laura Donahue, an important court decision last week on the Patriot Act. Tell us what this appeals court found.
DONOHUEYeah. So the Section 215 of the USA Patriot Act allowed the government to collect records. It was called the tangible goods provision. It could collect tangible goods where the government could show that there were reasonable grounds to believe that it was relevant to an authorized investigation. And what the court found was that language mattered. The reasonable grounds to believe that it was relevant was being read by the NSA and others in a way that understood relevance that everything, all telephony metadata is relevant to authorized investigations generally, therefore, for the past 7 or, no, 9 years, I guess -- 9 years, they've been able to collect telephony metadata in order to then look at that data and try to find patterns and try to identify potential threats to the United States.
DONOHUESo the court said that if everything is relevant, then nothing is irrelevant and so it's a violation of that statute to say that all telephony metadata is relevant.
PAGEYou've talked about metadata several times. Just tell us, briefly, what metadata refers to.
DONOHUEMetadata in the FISC order, in the foreign intelligence surveillance court order authorizing the telephony metadata program refers to the numbers that are dialed from a telephone, the numbers that dial a telephone and something called trunk identifier information, which is basically the local cell phone tower that one hooks up to in the course of making a telephone call. And any other relevant metadata related to a telephone call that one makes or places from one's cell phone.
PAGESo it tells you who made a call, how long it lasted, but it doesn't include the content of the phone call.
DONOHUENot the content. The thing about metadata, though, is it's actually, in many cases, even more revealing. In fact, Hayden said at one point, we kill people based on metadata and we've had other government officials say that metadata is very revealing because of the contextual information it provides. So it's not just who you call, but if you call a rape crisis hotline, if you call a democratic party headquarters. And then, patterns in phone calls so if you called different numbers in succession, a lot of information can be revealed, even though this is metadata.
PAGEBenjamin was this the first time a court had weighed in on whether this provision was legal?
WITTESIt's the first time an appeals court had. There had been two district courts, one here in Washington, that had ruled that the program violated the Fourth Amendment. That's on appeal to the D.C. circuit. And the lower court, in this case, had upheld the program on -- that this court then reversed it. So there had been previous lower court rulings.
PAGEBut this court did not -- the court decision didn't call it unconstitutional. Is that right?
DONOHUEThey called it illegal.
WITTESCorrect. So in order to decide whether something is -- before you decide whether something is unconstitutional, you normally decide whether it's, you know, authorized by statute at all. And so what this court said is we don't need to decide the constitutional question because we find that it doesn't -- isn't authorized by the Patriot Act, that the government was claiming as its lawful basis.
PAGEDevlin Barrett, the court also didn't stop this program from continuing. Why not?
BARRETTWell, because it's about to expire. The law itself, that everyone's arguing about, expires June 1 and the court essentially said, you know, look. We understand there's a debate in Congress and we're willing to not change things ourselves while Congress tries to decide what to do next. The challenge, I think, is that Congress seems to be very divided on this and it's not clear at all that Congress will do anything. And if Congress can't agree, then the law expires.
PAGEWell, I saw that Mitch McConnell, the Senate majority leader, yesterday, in an appearance at the Edward M. Kennedy Institute outside Boston argued that what they should do is just re-up the law, not revise it. If they do that, does it still make it vulnerable to the same kind of court challenge that the old law faced?
BARRETTWell, it does, but we still don't know because this court wouldn't actually address the constitutional question, presumably if McConnell has his way. You'll get to a situation where the courts have to come back and readdress the constitutional issues as, does this violate people's privacy.
PAGESo here's a question I think a lot of Americans would have. Has the use of this, this mass collection of telephone metadata, has it, in fact, made Americans safer over the past decade? Laura, what's your view?
DONOHUEWell, this was actually a point of some contention in Congress. And Senator Leahy really took the lead on this in many ways to try to drive home an answer and in the end, the government was only able to provide one instance where anybody was identified through this program that hadn't already been identified through other programs. And that one person, it was only two months afterwards, Vasili Mosalla (sp?) who was a cab driver in San Diego who had given some money to an al-Qaeda affiliate overseas so it was a case of material support that was identified.
DONOHUEAnd this is after nine years of collection all Americans' telephony metadata. This was considered to be -- it wasn't the smoking gun that was initially claimed by the government in defense of Section 215, the Section 215 program.
PAGEBenjamin, do you agree with that?
WITTESWell, so it is definitely true that the government has struggled to produce examples where you have, you know, attacks that would've happened but for the use of this data. On the other hand, when you talk to people who, you know, in government, in the security space, that's not really the metric that they measure intelligence programs by. As a general matter, we tend to think of these things as happening, you know, with what lawyers call but-for causation, right?
WITTESAnd in an intelligence community, that's not really the way they work. They tend to gather everything they can gather, pour it into a big pot, stir it and then they get this soup, right? And the soup either tastes good or it doesn't. It either produces good outcomes or it doesn't. And if it tastes good, it can be very hard to figure out what the role of a particular carrot or a particular piece of beef was in the good outcome.
WITTESI don't think most people in the intelligence community regard this as a critical or sort of one of their bread and butter programs. It's not like, you know, FISA 702, which is, you know, another program that has been very controversial, which is huge. This is a small program. It involves about 300 seed queries a year, but most people regard it as useful, you know, not groundbreaking, not earth-shattering, but useful.
WITTESOne other dimension of it that's important. The program was created to fill a very particular gap that arose in the context of the 9/11 case, which was people from abroad calling people domestically. And so a lot of people in the government regard it as a kind of insurance policy. You don't hear things on this program and that suggests that that gap in our previous intelligence collection authority is not being exploited. So I would not say it's an essential program. I would not say it's, you know, one of the most productive programs the government has, by any means.
WITTESOn the other hand, people feel better knowing it's there.
PAGEMichael Morell, the 33-year veteran of the CIA whom I interviewed on Friday, said that if this program had been in affect before 9/11, it is likely that intelligence agencies would've been able to see that there were these 19 hijackers communicating with one another. Laura, you're rolling your eyes.
DONOHUEYeah. So this -- you frequently hear this if, if, if. Basically, what this program does is it allows the government to collect the telephony metadata of all Americans and then to troll through that data and to look for patterns and associations and relationships. That is deeply problematic from a liberty perspective and certainly from a Fourth Amendment privacy perspective. This allows the government -- in fact, in the FISC order, even entirely domestic conversations.
DONOHUESo when the PTA president calls one of the mothers in the classroom, that's picked up by this program. And, from this, you can build very detailed social network analytics of who is connected with whom, which people are the powerful institutions in these networks and then any potential opposition can be headed off. And this was exactly what was underlying a program that USAID tried to put into place in Cuba called Zunzuneo where they tried to build a social network and then use that social network to overthrow the government.
DONOHUEYou know, the kind of power that's represented by these programs are not innocuous and certainly when legislatures like Senator Leahy looked at this and said, against this potential power that you're giving the federal government over every individual in America, you have only one case in nine years where this was even -- that this actually indicated activity that we didn't know about beforehand, this is an easy case.
DONOHUEYou know, this program, first of all, is illegal, as a statutory matter. It violates the statute. It's also unconstitutional.
PAGEDevlin, what do you think?
BARRETTYeah. And just to the 9/11 questions, while Morell have a point there, the reality is there were a whole bunch of missed things that went into not stopping 9/11. And it's fine to say, I think, as sort of a theory, frankly, that if we'd had a program like this, we would have had a better shot at doing it, but it's also true that if the FBI and CIA had done any number of things, it could have, you know, in theory stopped it earlier.
BARRETTI mean, the one thing that I find odd about that argument is that it sort of assumes, well, we don't have to change anything we do. We just need to get more of your stuff.
PAGELaura.
DONOHUEThe purpose of the Fourth Amendment when it was enacted was to protect against what's called a general warrant. A general warrant is an order issued by a court that doesn't specifically name the individual under investigation, the crime being alleged and hasn't -- nobody's established probable cause before the court as to this crime. This is basically a general warrant. A general warrant was, at the founding, absolutely rejected by the founders and this is really what we're seeing is a renewal of this without any specified crime and it gives the government an opportunity to find criminal activity and then to prosecute it. This is rather the cart before the horse.
PAGEWe're gonna take a short break. When we come back, we'll talk about a proposed compromise that's moving forward in the house. We'll take your calls. Our phone lines are open, 1-800-433-8850. Stay with us.
PAGEWelcome back. I'm Susan Page of USA Today, sitting in for Diane Rehm. And with me in the studio this hour, Benjamin Wittes, senior fellow in governant studies at the Brookings Institution. He's coauthor of "The Future of Violence." And Laura Donohue, she's a professor at Georgetown University Law School where she is also director of The Center on National Security and the Law and director of The Center on Privacy and Technology.
PAGEAnd Devlin Barrett who's a reporter. He covers the Justice Department for The Wall Street Journal. Well, Devlin, there is a proposal for a revised law. It was passed, I guess, it got through the House Judiciary Committee last week.
BARRETTThat's right.
PAGEHow would it differ from the current law?
BARRETTWell, the revised proposal would essentially take the data base, this giant inventory of calls to and from, out of government hands. And they would -- it would essentially say, you can search what the phone companies have, but you can't hold your own database. The politics of it are very tricky. A bill similar to that failed in the Senate last year. And it's, you know, one of the things that sort of fascinating about this new decision is, does this change any votes? It may, but it also may not.
PAGEIt would both change who holds the data. It would change…
BARRETTRight.
PAGE…the way in which the -- what the government would have to do to search the data, is that right? What would that require?
BARRETTWell, technically, the Obama administration has already put in place changes that require a judge's approval to do specific searches of the data. So that part has changed. But one of the most, you know, sort of controversial and from a privacy advocate's point of view, problematic pieces of the current law is that the government has a database of your phone calls.
BARRETTAnd this would essentially say, okay, you know what, the government is not going to be in the database -- in the phone call database business anymore. And if they want that information, if they want to cross reference that stuff, they can search what the phone companies possess, not what the government possesses.
PAGEAre the phone companies enthusiastic about…
BARRETTNo. No.
PAGE…the prospect of holding this data?
BARRETTHardly. I mean they, you know, the relationship between phone companies and the U.S. government has been a -- is a long established on. It's not like Silicon Valley where there's a lot of tension there. But this issue has created tensions where there were not tensions before.
PAGESo, Laura, does this address -- this revised law -- I guess it's called the USA Freedom Act.
BARRETTCorrect.
PAGEWould it address some of the concerns you have about the current Patriot Act provisions?
DONOHUEYes, it would. The problem is right now the assumption is you're guilty until proven innocent. They collect all the information and then they look for criminal activity. The FBI currently is searching the Section 215 database for utterly unrelated criminal matters, looking for potential criminal activity. What this would do is it would say no. First, you have to suspect somebody of wrongdoing. And then you can go after the information. And that certainly is a step in the right direction.
PAGEDo you think so, too, Benjamin?
WITTESSo I actually think there's a lot of agreement around -- among people who are, you know, whatever their politics, that, you know, some of reform of this set of programs is a good idea. And I have my anxieties about the USA Freedom Act, but basically I think it is better to pass it than not to pass it. And ironically, it could end up giving NSA access to a broader array of data than it currently has because under current law the NSA acquires and keeps in its own database everything that the telecommunications companies provide it.
WITTESBut there are holes in it, largely the result of cell phone use. And under this, the companies would keep their own data and NSA would get it when it needs it. And so I think it has the opportunity to create broader civil liberties protections that people like Laura will be enthusiastic about, but also broaden coverage in ways that may improve the performance of the program.
PAGEDevlin, it also provides for a little more transparency.
BARRETTRight. And part of the interesting dynamic that the court decision brings up is so if Congress never intentionally authorized this program, it's gonna be very hard to argue going forward that Congress is not now -- what -- if it authorizes anything, is not now intentionally authorizing what we essentially know to be going on. So there is more transparency, in theory, in place in the law.
BARRETTBut, look, you have to think about how will this actually work in practice, how will the FISA court, the intelligence surveillance court work in practice with a new set of rules? I think those are, in some ways, unknowable yet.
WITTESSo I…
PAGEBenjamin?
WITTESSo I do think the decision last week really stands to change the legislative landscape over the next few weeks. Until the court ruled last week, Senator McConnell and his allies were stopping movement on the Senate, asking for just a clean, straight reauthorization of the existing law for the next five years. Now, a federal appeals court has said that that law will not adequately support the program.
WITTESAnd I think that may well cause -- and certainly in my judgment should cause some of those conservatives who are -- have been holding up the bill to say, wait a minute. The cost of standing on that principle may be that the program disappears all together.
PAGEThat may be the case, but it was just yesterday that Mitch McConnell said in Boston, that the measure was an important tool to prevent the next terrorist attack. He said he would continue fighting for it against recent challenges. So that doesn't sound like his mind has been changed.
WITTESI agree with that. They were two votes away in the Senate without a ticking clock, from moving the thing forward. Now we're three weeks away from, you know, from expiration. It is important to emphasize the intelligence community supports the legislation. The president supports the legislation. So there's a very good argument, not grounded in civil liberties, but grounded in, hey, this program's gonna disappear in a puff of smoke if you don't do something. This is not a terrible compromise.
DONOHUEAnd I agree with Ben. He's raising good points. And I would add to that, there's something called a counterterrorist spiral, which is whenever liberal democratic states introduce counterterrorist provisions, often the most egregious ones are made temporary, with the idea that in the future if they don't need them they can be rescinded. They are never rescinded. So in my first book I looked at the U.K., where for 150 years they had temporary counterterrorist law.
DONOHUEThe U.S. is no different. They USA Patriot Act, 14 of 16 provisions were temporary, 2 were indefinitely continued. Here we again have a temporary one. And the reason why they're never rescinded is because in order to rescind them you have to prove either that violence is no longer possible, but of course terrorism is always possible. Or that some level of violence is acceptable. So whoever tries to rescind it, then it has the responsibility of the next attack.
DONOHUESo McConnell's discourse fits into this pattern, which you see again and again and again, both in the United States and the United Kingdom, that once you have a temporary provision the fear is that by withdrawing it, that you'll be responsible for the next attack.
PAGELet's go to the phones and let our listeners join our conversation. We're gonna start with Bert. He's joining us from Washington, D.C. Bert, you're on the air.
BERTThank you. Two important points. One, Laura, a few minutes ago, made the really key point on intelligence oversight when she said that there -- in this case, going without any evidence of wrongdoing or basis for suspicion to looking at everything to see if they can find it, what that's in echo of is what happened under Lyndon Johnson and Nixon, when Johnson couldn't believe that the opposition to the Vietnam War would be -- could be so indigenous.
BERTAnd he pushed the CIA and FBI to find how the Soviet Union was controlling it, which I investigated for the Church Committee. Instead of just seeing some basis for suspecting someone, they looked at people who were prominent in the movement and investigated the heck out of them to see if they could find a connection. That's what 215, at bottom, is. And the second point is that the -- what it really illustrates is the need for much stronger Congressional oversight.
BERTPresident Obama, and very recently, the chair of the intelligence committee said of course this law authorized what they're doing. I was there when it was drafted. And the fact is that the entire House Judiciary Committee from far left to far right were astounded when they learned that they were interpreting 215 to allow this kind of bulk collection. And the former staff of the Church Committee have proposed -- and there will be an anniversary event at the end of May -- a new comprehensive review of how well our intelligence system is working and the need for much stronger Congressional oversight.
PAGENow, Bert, I think that other -- some people on the panel have recognized your voice, but why don't you tell the rest of us who you are, 'cause clearly you've got a deep background in this area.
BERTWell, I was in charge of the investigations of the CIA for the Church Committee. Then I was counsel to President Carter for oversight of all U.S. intelligence agencies. And finally, I was senior counsel on the House Judiciary Committee when the Patriot Act -- when this was added to the Patriot Act and other intelligence reforms were made to FISA.
PAGEWell, thanks very much for your call. I'm always impressed by the quality of the listeners to "The Diane Rehm Show." I think Laura would like to make a comment and also Benjamin.
DONOHUEYeah, sure. First of all, it's a pleasure to meet you, I have to say. So, and thank you for calling in. I wrote a brief on behalf of many members of the former Church Committee for this case, actually, that was just handed down last week. And the court looked to the Church Committee's experiences and their recommendations. At that time, as you will recall, Project MINARET and Operation Shamrock -- there were a number, in addition to the CIA programs, and obviously CHAOS, and CONUS, the Army's CONUS.
DONOHUEThere were many programs underway. And the Foreign Intelligence Surveillance Act was introduced to respond to overreach by the NSA and others. And at that time General Lew Allen, who was the director of the NSA, tried to convince Congress that the NSA should be allowed to collect information, as it was doing in Shamrock and MINARET, and then analyze the information. It was only the analysis of the information that implicated Fourth Amendment.
DONOHUEAnd Congress said no. It's the time at which you obtain that information, that the Fourth Amendment privacy rights come into play. And FISA was the way in which the foreign intelligence Surveillance Act was Congress's way of responding. That is the legislation that we're currently considering. And the NSA is again making this argument that we can collect the information and then search it. And once again, the court came, you know, well, the court hasn't ruled on the Constitutional issue, but the question is, can the NSA obtain all Americans' information and then look for wrongdoing?
DONOHUEAnd the answer to that question, as a Constitutional matter, is no. Now, one point that I do want to bring up, Bert, because in 1978, when you part of the introduction of the Foreign Intelligence Surveillance Court, one of the things that the USA Freedom Act is it produces the possibility of an advocate at the court so that the court will have adversarial counsel.
DONOHUEThe Foreign Intelligence Surveillance Court was never meant to be kind of a court that would consider the detailed Constitutional questions and that its decisions would act as precedent and stare decisis would go into play. It was simply meant to grant warrants or not grant warrants when the government had demonstrated probable cause that a target was a foreign power or an agent of a foreign power.
DONOHUEAnd so one of the most important aspects of this legislation that we've already discussed is that it would introduce adversarial counsel so that the court would have the benefit of contrary views when it was considering whether either as a statutory matter or a Constitutional matter a request from the NSA should be met.
PAGEBenjamin?
WITTESSo I mean I think, you know, Bert makes some very good points. But I do want to push back a bit against the comparison in his remarks and some of Laura's remarks and in the court opinion itself, between the current era and the 1970s era that gave rise to the FISA court in the first place and the Foreign Intelligence Surveillance Act. You know, this program, there are legal questions around the authorization of the program. Laura has argued, and others have argued, that there are Constitutional problems with the program.
WITTESThere have not been abuses of this program. This has not been a program where, you know, Americans' data has been vacuumed up and compared, you know, done general pattern analysis. It is a very narrow program. Everything gets collected. Material is quarried only when there is a very specific, what's called a reasonable, articulable suspicion. And very, very few people have access to the data. It's not a generalized search program.
PAGEBert, thanks so much your call. You're listening to "The Diane Rehm Show." We're gonna go back to the phones, 1-800-433-8850. Devlin, first I want to ask you, do you think the landscape has changed enough in the wake of this court decision last Thursday, that this compromise that's going -- we're moving through the House, will in fact not only get to the House as expected, but also get through the Senate?
BARRETTYou know, I actually don't think the court decision will change many votes. I think the ticking clock will -- may change votes. But, you know, what was striking to me -- Ben brought this up earlier. But what was most striking to me about the Republican reaction to the court decision was how many senior Republicans said, well, this is just one court making one decision. I -- I'll be honest, I do not view the Second Circuit that way. I also do not view a 3-0 decision that way.
BARRETTI do not think that that's a good reading of where the court is headed, and courts generally are headed on this issue. But having said that, it doesn't seem to have affected the political will of the Republicans who don't want to do the reformed version. So I think this has more to do with the clock. And I think if, in the end of the day, what may happen is they may go -- they may sue for peace, in terms of supporting the reformed version if they think the only other alternative is the death to the whole thing.
PAGEIs it possible that it expires, that there's no deal? Congress often has been unable to act.
BARRETTOh, I think it's very possible. I think you could have a situation where, in theory, the Senate votes for a pure reauthorization of it, the House votes for the reform. Neither side is willing to cave on that. And so the whole thing just dies.
WITTESYou could also have a situation in which the Senate and the House compromise on a very short term extension in order to give themselves more time, but then you're left in the situation where the underlying program has this, you know, A, another ticking clock and B, the legal cloud of the Second Circuit's opinion. So it's an area where you would really want Congress to be more functional than it has been as a general proposition over the last few years.
PAGENow, some other provisions of the Patriot Act also would expire at the end of the month. Devlin, tell us what those are.
BARRETTWell, there's one called the Roving Wire Taps Provision, which is -- to be honest, it's just to try to get around some of the mechanics, in my view, of chasing particular suspects, in that, you know, people have different phones, people have multiple different ways of communicating. And the other is essentially the -- what's often referred to as the Lone Wolf Provision, which is we are, you know, essentially authorizing surveillance and investigations of people for whom there is no apparent connection to an established organized terrorism group.
BARRETTThat's becoming, frankly, more and more relevant in the -- in an era of ISIS operating over Twitter. But frankly, I don't think either of those provisions raise the kind of concerns that the phone program does or, frankly, some other programs do that aren't, you know, on the table right now, let's say.
PAGELaura?
DONOHUEYeah, one thing to remember is that many of these programs that have been put into place were a way of trying to find a legislative fit for programs that President Bush put into place just after 9/11, under what some people call Terrorism Surveillance Program, TSP, which involved the collection of internet and telephony content and metadata. And they tried around 2004, 2005 to try to find ways to put this into a statutory framework.
DONOHUEAnd it just isn't a good fit. Right. So the idea that this, the telephone metadata fits into the tangible goods provision, that it required the court to find that all telephony metadata is relevant. Well, so is all financial metadata and so are all library records and all gun records and all educational records. All of that might be potentially relevant to a counterterrorism investigation.
DONOHUEYou know, this kind of distension of the language that occurred to try to keep this program alive is deeply concerning. So, you know, the idea that Congress would actually eliminate Section 215, I think, is an entirely reasonably way to respond to that concern.
PAGEWe're gonna take another short break. When we come back we'll go to the phones. We'll read your calls and comments. You can send us an email at drshow.org. Stay with us.
PAGEWelcome back. I'm Susan Page of USA Today, sitting in for Diane Rehm. And with me in the studio this hour, Devlin Barrett of the Wall Street Journal, Laura Donohue of Georgetown University Law School, and Benjamin Wittes of the Brookings Institution. You know, we have two emails I'm going to read that are like sides of a coin. Here's the first one, it's from Kay, who writes us in Dallas, she writes, "I am an Air America widow. My Air America husband was killed in action flying in Laos in 1970. I believe in the fourth amendment. My husband died for America and for the Constitution.
PAGEThat said, the CIA and FBI need all the help they can get to keep us safe. Don't have blood on your hands by hamstringing Congress. Yes, politics are always at play, yes, no other country is as free as and transparent as ours. Not perfect, but the best place to live free." And yet, here's another email we get from Pam, who writes us from New London, New Hampshire. She writes, "how many people have died defending our rights? I'm not willing to give up those tragically purchased rights just for the government to have one more tool in the box." And she also writes, "Don't you think that the terrorist know that all conversations are monitored? Why would they use a monitored system to plan anything?"
PAGEYou know, here are two of our listeners, both arguing that Americans have died defending out rights, but coming to very different conclusions about what that ought to mean for this debate.
BARRETTWell, yeah, and I think part of what's so difficult about this debate is -- and officials have spoken to it repeatedly, which is, how far are you willing to go to save lives? And that's really sort of what this all comes down to. And frankly, which lives? And that is a hard choice to make, and in the context of terrorism, that is an incredibly heated debate a lot of the time.
WITTESAnd part of the question is also, you know, to say that we shouldn't give up our rights, I think everybody agrees with, or at least most people agree with. But that doesn't answer the question, what the substance of those rights are. And you know, the idea that the government could have a database of all metadata, or a lot of metadata of phone calls within and outside of the United States is an idea that's so new, it's so improbable earlier in our history that it could exist, that the question of how that interacts with our rights is actually not an obvious one.
PAGEYes, Laura?
DONOHUEI actually don't think this is a new question at all. This was James Otis and Paxton's case. The British started serving writs of assistance on the United States, or on the colonists at the time, which allowed the British government, the crown officers, to go into anybody's home and to collect a person's private papers, affects, information, business records, and to look through these for potential wrongdoing. And James Otis gave this fiery oration that John Adams, our second president -- he was present at the time -- he later wrote, "then and there, the child independence was born."
DONOHUEYou know, that was the first shot of the Revolution. You know, we fought a revolution over establishing the right of people to be protected within their own homes from undue government intrusion and interference. And that is not a new issue, whether it's done in a digital age or whether it's done in the age of the Pony Express. That is something that Americans have the right to, that we have fought hard for, and that is part of our Constitutional heritage and our fortune.
BARRETTBut I do think something has changed in the digital age. I do think the way you can take date, the scale at which you can take data, and the way you can cross reference that is just something we have to spend, as a country, a lot of time thinking about. And that's not just phone records. That's, look, that's license plate readers, which are everywhere now. What do you do with that information, what won't you do with that information? That's, as we've been talking about, all your internet activity what is takeable, what should be takeable, what should be getable?
BARRETTThere's a ton of ways in which the government has been able to scale up its ability to look at our lives, and frankly, those are conversations that are worth having.
PAGELaura?
DONOHUEYeah, I entirely agree with that. We live in a digital age, and so in order to do this, both the courts and Congress need to really grapple with what privacy looks like in this world in which we now live. In 1967 was the last seminal case and really Fourth Amendment doctrine where a listening device was attached to the outside of a telephone booth. And for the first time, the court declared that the Fourth Amendment protects people, not just places. So it's no longer tied to the place itself. We're at a Katz type moment. There was a case two years ago called Jones, where somebody attached a GPS chip to a car.
DONOHUEAnd Justice Scalia, writing on behalf of the court, used trespass doctrine to say, well, this was outside the ten day window provided by the courts, and therefore, for 28 days, while this car was followed around with this GPS chip, that was a trespass on the car. But a shadow majority of the court at that point said that this also violated the reasonable expectation of privacy, and Justice Sotomayor went so far as to say that she would overturn what we refer to as third party doctrine, because of the way in which ubiquitous surveillance has a deeper privacy implication in a digital age.
PAGEBenjamin.
WITTESSo Laura just inadvertently, or in passing, referred to the case that actually establishes that this material is generally not Constitutionally protected. In the late 1970s, the court, confronting the issue of telephony metadata, decided that this was material that individuals voluntarily give to a third party, which is to say to their telephone companies for billing purposes. Once you've given them up, you don't have a reasonable expectation of privacy in them. And so the court actually disagrees with Laura that this is the issue over which we fought a revolution. I'm skeptical myself that John Adams would have been especially worked up about telephony metadata. I don't think that's a knowable question.
WITTESAnd so I think what we need to do is, we need to figure out both as a Constitutional -- as a matter of Constitutional doctrine, but also more importantly, as a set of normative expectations reflected in statue, what we want government to be able to do with this type of data, what kind of data we want to collect, what kind of data we don't want to collect, what we want to protect, and that's why debates like the discussion over the USA Freedom Act are so important.
PAGEYou know, I'm struck, though, by trying to seek a balance, which is what our Constitutional system often tried to do, privacy and security -- how that is shaped by the political moment. So, in the wake of 9/11, the Patriot Act was passed. Now that that threat has seemed to recede for a decade, more interest in revising it. We see the rise of ISIS now, I think that's alarmed a lot of Americans and maybe changed their calculation. To what degree does this reflect kind of what else is happening in the world, Devlin, this debate on the Hill.
BARRETTI don't think you can escape it. I think everything is in the context of its time, and look, I think it was hard enough to have the debate in October 2001 when the Patriot Act was passed, before you knew what you were debating about. You know, one of the big issues here is it took, you know, if you count from, say, 2005 on, it took roughly ten years to even understand the basic parameters of just the phone surveillance program. It is hard to have these debates when you're talking about intelligence secrets to begin with. And so it's all in the context of its time. I think if there were, God forbid, another major attack, that would again shift the landscape on which we talk about all this stuff.
PAGELet's go to the phones and talk to David. He's calling us from Ft. Myers, Fla. David, thanks for joining us on "The Diane Rehm Show."
DAVIDHi. My question, or my -- yeah, my question would be, how would this have gone down when President Nixon was president for the time that he was president? And what would -- how would it have affected individuals either knowingly or unknown to them?
PAGEAll right...
DAVIDAll right.
PAGEDavid, thanks so much for your call. Benjamin?
WITTESSo, look. That's an excellent question. And this is part of the reason that I think it's important to distinguish between what's going on now and what was going on in the '70s. There is no doubt that this sort of database is enormously powerful. And if you imagine an abusive president, and an abusive FBI director, and an abusive intelligence community with uncontrolled, un-overseen powers of this kind of data, that's a very terrifying thing. And the question is, whether your response to that is A, to put restrictions on it, B, not to have it at all, or C, sort of to engage in very rigorous oversight.
WITTESOur traditional answer over the last ten years has been, do the oversight, allow the activity, and we have not seen abuses, but it is certainly possible that in a different environment, we could.
DONOHUEYeah, I'm just not understanding this, that we haven't seen abuses. Like we'll set LOVEINT aside. We actually have a (word?) for the use of this database to check out potential dates, which actually has already occurred with the NSA. The inspector general reports show that not only that has occurred, and actually the court opinions, but the NSA has been routinely abusing this power. They've been querying it without reasonable articulable suspicion, so much so that in 2009, the court found out that of 19,000, almost 19,000 inquires, almost 1,000 sum odd, only 1,000 sum odd has reasonable articulable suspicion attached to it.
DONOHUESo, in more than 17,000 queries of this database, the NSA was querying it outside what the court had told it to do. And part of the problem here is the Foreign Intelligence Surveillance Court has abdicated much of its oversight to the National Security Agency, and again, this is not a new question. You know, you do not have the fox guard the henhouse. You don't have the NSA responsible for determining when it has reasonable articulable suspicion to query such a powerful database. So the Foreign Intelligence Surveillance Court needs to be in a position where it does exercise direct oversight. And something that we haven't touched on yet is technological expertise.
DONOHUESo the court does need an advocate to consider contrary views to the government's when positions are put before it. But it also needs access to the technological expertise so that it can perform its oversight function effectively.
PAGEBenjamin.
WITTESSo, first of all, I mean, there certainly have been errors, and there have been errors that have produced significant dialogues and back and forth between the FISA court and the agency and the Justice Department. In none of those cases has the court found -- some of which, by the way, involve very extensive litigation records that have now been declassified. In none of those cases does the mistake seem to have been intentional or was it a politically driven abuse of the type that the caller was referring to. The answer seems to have been that these are complex human systems and they involve errors sometimes, and that has certainly happened.
PAGEHere's an email we got, which says, "why the outcry over government metadata? The IT market collects and sells metadata all the time."
BARRETTThat's absolutely right, and they do it in many ways more feverishly, more intently than the government does. And you can sort of observe that in real time just by looking at the pop up ads as you browse around the web. But...
PAGEWell, they seem to know what it is you want to buy.
BARRETTRight, they seem to have a very good idea of what it is I want to buy. And even some things I don't want to buy. But I think, look, I think a lot of this debate centers around a basic question of -- which is, you know, for the intelligence community, their attitude is, trust us. And there -- what you're seeing now is an argument about, how do you prove that you are worth trusting, and look, for a good part of this government was based on the principle that the government shouldn't be trusted.
DONOHUESo, one of my colleagues at Stanford, Scott Sagan, wrote one of the best titled papers of all times, in which he looked at the more redundancies you build into a system, the less effective they become. And he titled the paper, "The Problem of Redundancy Problem." And the response to this is not more oversight, the response is more effective oversight, more robust oversight, and that's what's required.
PAGEHere's an emailer, Michael, who asked us, "if the metadata trail indicates possible wrongdoing, can the government then access the actual content of phone messages?"
WITTESThat's an excellent question, and the answer is no. not because -- not for legal reasons, but because the metadata database actually does not presumptively capture that information. So what the government can do if there's, you know, evidence that, for example, Laura has called me and I'm a terrorist, is that it may, that may then be the basis for a FISA warrant against Laura, but it's not -- the contents of our previous communication, unless it was otherwise captured, is not part of that database.
PAGEI'm Susan Page, and you're listening to "The Diane Rehm Show." Let's work in another caller, let's go to Burlington, N.C., and talk to Greg. Greg, thanks for holding on.
GREGThank you. I just (unintelligible).
PAGEGreg, it sounds like you're on a cell phone and we're having trouble hearing you. So let's go instead to Constance who's calling us from Bethesda, Md. Hi, Constance.
CONSTANCEHi, good morning. Thank you for taking my call. I just wanted to say something. There's an average of ten kids that die each day of gun violence in the U.S. It's a daily horror, and it's a real daily threat. So I know there's also outside terrorism, but ten kids today is completely wrong. So can there be an effort from the intelligence community to change this?
PAGEAll right, Constance, thank you for your call. And of course, a concern to all of us. Devlin?
BARRETTAnd the caller points out one of the things that is sort of an oddity of the debate, which is, in a lot of the debate about terrorism, we are arguing about, as a statistical model, something that is less deadly than many other threats in the United States. And you know, there used to be this view that, well, police can -- the more the police look at terrorism, the more they would look at crime. There's not a lot to back that up. And I do think that one of the things that the government is sort of poor at discussing a lot of time is, why is, for lack of a better term, a loner with a gun for ISIS who kills someone significantly worse, and more trouble than a loner with a gun who kills someone for some other horrible cause.
BARRETTAnd I don't think the government, frankly, has good answers on that on many days. But, look, the truth is, terrorism is designed to spread terror and cause fear, and terrorist attacks cause fear publically in a way that other violence simply does not.
PAGEWe know about the reach of this program because of the disclosures that Edward Snowden made about two years ago. And I wonder, you know, big debate about Edward Snowden and did he provide a public service or was he guilty of treason? I just wonder if the three of you could just very briefly say what your view is of Edward Snowden and his actions. Start with you, Benjamin.
WITTESIt's a hard question. I mean, I -- if Edward Snowden had revealed the existence of this program and nothing other than this program, I would feel, might feel very differently about him, honesty, because I do think this is a debate that needed to happen. The problem with Edward Snowden is he revealed an enormous amount of information other than programs like this that not much of which has no civil liberties or public policy implications at all, but are hugely damaging to intelligence operations.
PAGEWe're almost out of time, just very quickly, Laura.
DONOHUEYeah, it's hard to think how we couldn't have had this debate seven years ago, eight years ago, nine years ago, which is when this debate should have happened. For the Snowden releases, for what he released, it was illegal what he did.
PAGEAnd Devlin?
BARRETTI think in some ways the system built Snowden more than Snowden reacted to the system. I think, you know, I have talked to innumerable government officials who had concerns about this program and others, who felt there was no way to have an open, even in a closed system, have an open discussion of the right or wrong of it. So I think in some ways, Snowden was inevitable.
PAGELet me end with comments from two listeners. The first is a tweet from Rhonda, she writes, "The first question asked after something happens is, why didn't the government know about these bad people and stop them? You can't have it both ways." And here with a contrary view, Frank in Texas who writes us an email, "It is unbelievable that we are debating whether living in an Orwellian society should be fine. This will get worse as government intrusiveness becomes ever more acceptable, and government spying capabilities grow." Two very different views there.
PAGELet me thank our panel for being with us this hour. Devlin Barrett of the Wall Street Journal, Laura Donohue of Georgetown University Law School, Benjamin Wittes of the Brookings Institution. Thanks so much for being with us.
BARRETTThank you.
DONOHUEThank you very much.
WITTESThanks for having us.
PAGEI'm Susan Page of USA Today, sitting in for Diane Rehm. Thanks for listening.
After 52 years at WAMU, Diane Rehm says goodbye.
Diane takes the mic one last time at WAMU. She talks to Susan Page of USA Today about Trump’s first hundred days – and what they say about the next hundred.
Maryland Congressman Jamie Raskin was first elected to the House in 2016, just as Donald Trump ascended to the presidency for the first time. Since then, few Democrats have worked as…
Can the courts act as a check on the Trump administration’s power? CNN chief Supreme Court analyst Joan Biskupic on how the clash over deportations is testing the judiciary.